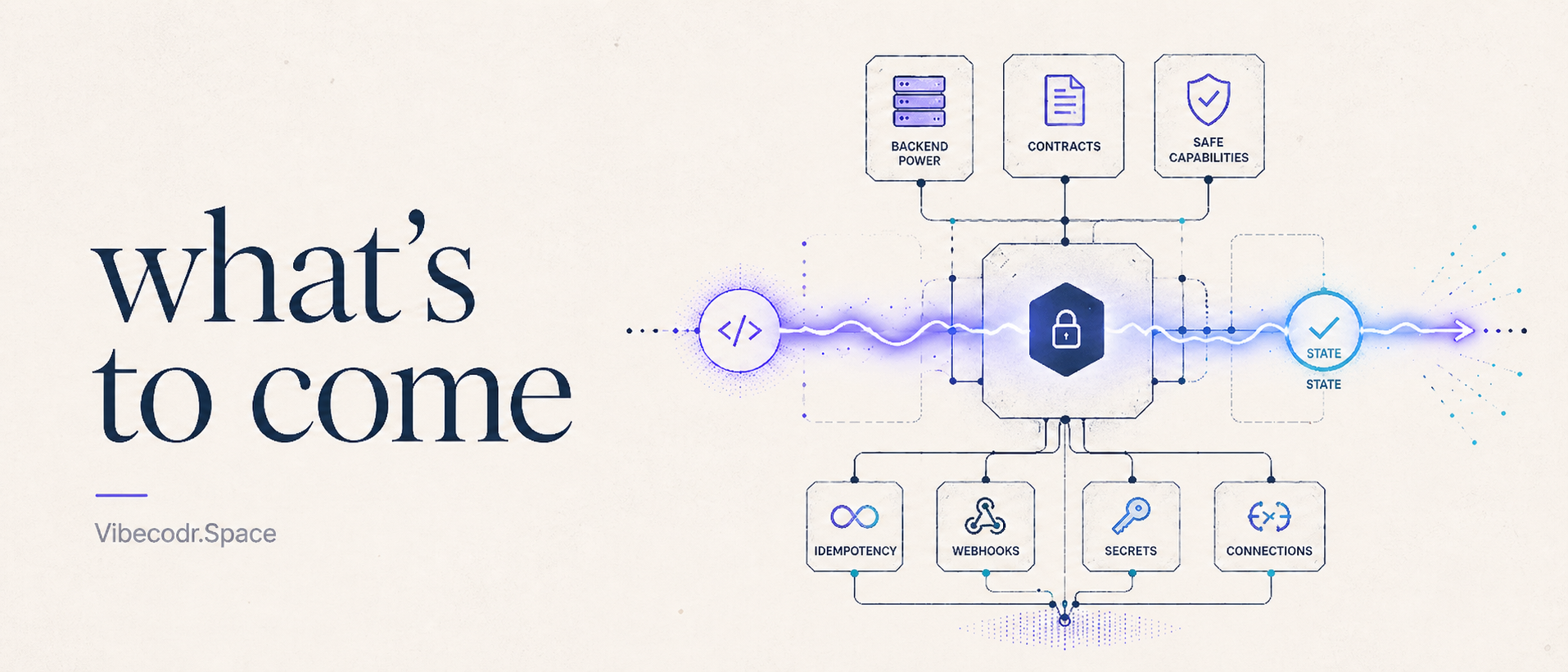
The next layer of Vibecodr is not just more backend power. It is a clearer contract for what a published vibe can safely become.
I have been spending a lot of time on a part of Vibecodr that is difficult to screenshot, which is usually a sign that the work matters. The simple product version is that Pulses should get better. They should let builders add backend behavior to the things they publish on Vibecodr, so a vibe can receive a webhook, call an API, use a secret, talk to a connected account, coordinate work, remember state, and do the small server-side things that make an app feel real instead of decorative.
The architecture version is more precise: Pulses need to become a runtime contract, not a pile of backend escape hatches.
That distinction is where most of the current planning work lives. Once user-created software moves from “runs in a browser sandbox” to “can perform backend behavior,” the question stops being only, “Can we make this possible?” It becomes a set of harder questions about authority, secrets, retries, duplicate execution, public examples, and whether every surface of the platform agrees about what a Pulse is allowed to do.
Who is allowed to do what? Where does the secret live? Which route is allowed to use it? What happens if the webhook retries? What happens if a handler runs twice? What happens if an agent generated the code from a stale example? What happens if Studio, the runtime, the docs, the CLI, and the deployment layer each learned a slightly different version of the same feature?
That is the real work ahead. Not making backend power exist, but making backend power legible enough, bounded enough, and dependable enough to belong on Vibecodr.
The problem with “just add a backend”
There is a very tempting path here: expose a database, expose environment variables, expose a worker, expose a fetch function, let advanced users figure it out, and call the result powerful. That path is fast, and it would probably make for a very clean launch sentence. It is also how platforms accidentally make beginners responsible for infrastructure before they even know which failure modes exist.
A database is not only storage. It is consistency, permissions, migrations, data retention, cleanup, quotas, and debugging. A webhook is not only an endpoint. It is signature verification, raw body handling, replay protection, retries, duplicate delivery, malformed payloads, and provider-specific behavior. A secret is not only a string. It is a boundary between private setup and public execution. A connected account is not only an access token. It is scope, expiry, redirect behavior, revocation, provider errors, and whether that credential can accidentally be sent somewhere it never should have gone.
If Vibecodr exposes all of that as raw machinery first, the platform becomes more powerful on paper while becoming less humane in practice. That is not the trade I want. The goal is not to hide complexity by pretending it does not exist. The goal is to put the complexity where the platform can enforce it, explain it, inspect it, and test it.
Pulse is the backend side of a vibe
The mental model I want is still small. A vibe is the experience people can open, run, share, embed, and remix. A Pulse is the backend behavior attached to that experience. A beginner might start with one tiny server function, while a more advanced builder might eventually have multiple routes, provider connections, state behavior, and real setup requirements. Both of those paths should feel like they belong to the same product.
The creator-facing model should stay close to this: write the smallest useful server function, put public config in .pulse, put private values in Secrets, use Connections for connected accounts, use env.fetch for policy-controlled outbound requests, use Pulse State when you need memory or coordination, and publish it like a vibe.
There is real infrastructure underneath that. Workers for Platforms, dispatch routing, generated wrappers, policy proxies, deployment metadata, and eventually state gateways and Durable Object-backed coordination all have a role to play. But that is the platform-facing reality. It should not be the beginner API.
The first thing to fix is truth
One of the easiest ways to make a platform feel unreliable is to let every surface learn the same feature separately. Studio learns one version. The runtime learns another. Docs learn a third. The CLI gets a slightly older one. Agents infer a fifth from whatever examples happen to be nearby. That sounds like obvious systems design, and in a calmer world maybe it is.
But when agents are part of the primary development loop, source-of-truth discipline becomes much easier to lose than people think. Agents are very good at helping you move quickly. They can add the route, update the UI, draft the docs, generate the example, and patch the validation path before you have fully noticed that each surface now contains its own private interpretation of the feature.
That is not a criticism of agents. It is a criticism of momentum without a spine. The faster the platform can change, the more important it becomes to decide where truth is allowed to live.
For Pulses, that place should be PulseDescriptor.
A Pulse might start as a default handler, use GET and POST exports, grow into a route table, or eventually use a helper like definePulse(). I do not want builders to write a giant manifest before they have made anything useful. But before publish, every supported authoring shape should normalize into one descriptor contract.
That descriptor should drive setup UI, runtime validation, generated examples, OpenAPI metadata, MCP surfaces, CLI guidance, local replay fixtures, cost and limit previews, and deployment decisions. If Studio says a secret is required, the runtime should agree. If generated docs say a route accepts a payload, validation should agree. If an agent sees a capability, it should be reading from the same source of truth as publish. If deployment rejects a missing setup item, the error should explain the fix instead of turning into a mysterious build failure.
The goal is not descriptor ceremony. The goal is to stop platform meaning from quietly forking.
The public SDK should not leak the engine room The next layer is the public SDK boundary, which sounds like cleanup until you realize how much trust depends on it. Internally, Vibecodr has to deal with real infrastructure names. There are deployment bindings, dispatch details, generated wrappers, grant headers, runtime metadata, compatibility paths, and storage concepts. Those things exist because the platform is real, but creator code should not see the engine room by accident.
A builder should see a small, Vibecodr-shaped runtime surface: input, env.pulse, env.secrets, env.webhooks, env.connections, env.fetch, env.log, env.request, env.runtime, and eventually descriptor-declared env.state resources. That is the surface worth teaching. Not raw internal binding names, physical storage names, grant headers, implementation-only Cloudflare details, or plan packaging constants embedded into type comments that agents will copy forever.
This matters because the public SDK is not just for humans anymore. It is also training material for AI-generated code. If the public types leak the wrong concepts, agents will repeat them. If examples use raw secrets as the happy path, generated code will too. A public SDK is a product surface, and it should teach the model we actually want people to build with.
Secrets should become capabilities, not strings The next phase is secrets, webhooks, connections, and egress. This is where “safe by default” either becomes real or becomes marketing copy.
The easiest version of secrets is get("MY_SECRET"). It is familiar, flexible, and sometimes necessary as a low-level escape hatch. It is also a great way to make the secret appear in memory as a raw string, pass through logs, get returned in a response by mistake, or get attached to a request that follows a redirect somewhere it should never go. Raw access may have a place for advanced cases, but it should not be the beginner path.
The better beginner model is policy-bound capability. A secret should be usable as a bearer token, header, query value, or verifier input without making raw strings the normal pattern. A connected account should be used through a provider-scoped connection surface, not copied into user code as an access token. A webhook should be verified before the payload becomes trusted. A credentialed outbound request should go through one policy path that can handle host allowlists, redirect rules, SSRF protection, private-network blocks, telemetry, and redaction.
That is a lot of system work for something that might look like a small helper in an example, but the example is the point. If the first Stripe webhook Blueprint teaches people to verify the signature before parsing trusted data, that becomes the default mental model. If the first provider integration teaches people to use a connection capability instead of a copied token, that becomes the default mental model. If the first authenticated fetch example uses policy-bound auth, that becomes the default mental model.
Blueprints are not just starters. They are product-shaped lessons.
State should start with behavior The most important future piece is Pulse State, and it is also the piece I am trying hardest not to overbuild in public. There are many things Pulse State could eventually mean: counters, sessions, jobs, locks, object state, rooms, maybe even user-defined backend objects. Those are exciting, but they are not v1.
The first state behavior should be narrower and more boring: idempotency. Prevent duplicate runs. That is it, and that is enough.
Duplicate work is one of the first real backend problems people hit once software talks to the outside world. Webhooks retry. Browsers resubmit. Networks fail after the server already did the thing. Providers send the same event again. Users double-click. A handler times out while the side effect still happened. If the vibe is only visual, that might be annoying. If the vibe is taking an action, it can be destructive.
So the planned first state protocol is a Claim Ledger: a platform-owned way to claim a key, run protected work once, complete or fail the attempt, and make duplicate attempts behave safely. The public version should feel simple: use runOnce() when this operation must not duplicate. The internal version is much more serious. It needs a State Gateway, deployment state manifests, invocation grants, claim capability tokens, route-scoped authority, stable resource ids, quotas, shard routing, lease expiry, fencing tokens, redacted key hashes, rollback modes, inspectability APIs, and conformance tests.
The builder should not need to understand all of that to use the beginner path. But all of that has to exist if the beginner path is going to be trustworthy instead of magical.
Magic is only comforting until it breaks.
Why idempotency comes before flashier things Idempotency is not a shiny feature, which is exactly why it belongs near the beginning. It is the kind of feature nobody notices when it works and everybody feels when it fails. A payment should not run twice. A webhook should not process the same event as if it were new. A form submission should not create duplicate work because a request retried. A provider mutation should have a stable external idempotency key where the provider supports it.
This is the kind of boring reliability that makes a platform feel calm. And calm matters. If Vibecodr is going to host runnable, remixable, public software, it cannot only optimize for the moment someone clicks publish. It has to care about what happens after the click, when the thing is used by someone else, retried by a provider, copied by an agent, or remixed by a person who starts from the patterns we taught them.
That is why idempotency gets the first seat. Not because it is the biggest future state feature, but because it is one of the clearest places where platform behavior can protect user intent.
The later work needs its own contracts
After idempotency, there are more protocols worth exploring: counters, sessions, jobs, locks, objects, rooms, and user-defined backend objects. Each of those sounds simple until you look closely. A counter is not just an integer. A session is not just a record. A job is not just a delayed function. A lock is not just a boolean. A room is not just state; it has realtime semantics, fanout, presence, lifecycle, abuse controls, and probably a different shape of Durable Object behavior than a claim ledger.
That is why I do not want to smuggle all of those into the first Pulse State launch under one vague “backend memory” umbrella. The shared kernel can be built with the future in mind, but the public protocols should ship only when their semantics are clear. That is how Vibecodr stays permissive without becoming mushy.
What “Social, Permissive, Safe” means here I keep coming back to three words for Vibecodr: Social, Permissive, and Safe. They are easy words to say. The backend runtime is where they become harder.
Social means backend behavior should be explainable and inspectable enough that people can share, remix, and learn from it. Permissive means builders should be able to make real software, call external services, use connected accounts, write custom handlers, and grow beyond toy examples. Safe means those powers should be explicit, route-scoped, policy-mediated, bounded, logged, and fail closed.
The tension is the product. If Vibecodr is only social and permissive, it becomes reckless. If it is only safe, it becomes sterile. The work is to keep all three alive at once.
Why write about this before it ships?
I am writing about this before it ships because this is the part of building a platform that is easy to make invisible. A feature page can say “backend functions.” A changelog can say “added Pulse State.” A button can say “deploy.” None of that explains the choices underneath.
It does not explain why env.db should be treated as advanced or compatibility instead of the first concept people learn. It does not explain why a descriptor has to become the source of truth before docs, Studio, MCP, CLI, and deployment can safely agree. It does not explain why secrets should be capabilities. It does not explain why state starts with idempotency instead of a big open-ended storage surface. It does not explain why examples are part of the security model.
If I do not explain those things, the product can start to look like a pile of constraints instead of what it actually is: an attempt to make powerful software creation feel safer, clearer, and more durable. I want Vibecodr to be transparent about that, not in a polished “trust us” way, but in a “here is what we are designing, here is what can go wrong, and here is how we are trying to make the safer path the normal path” way.
What is coming
The near-term direction is clear. First, clean up the surfaces that teach Pulses so stale examples do not become accidental product promises. Then normalize Pulse authoring through PulseDescriptor, so the platform has one source of truth for setup, validation, examples, deployment, agents, and docs. Then separate the public SDK from internal machinery, so creators see Vibecodr capabilities instead of implementation details.
After that, make secrets, webhooks, connections, and authenticated egress policy-bound by default. Then ship the first Pulse State behavior: idempotency through a platform-owned Claim Ledger. Only after the kernel proves itself should Vibecodr explore future protocols like counters, sessions, jobs, locks, objects, and rooms.
That sequence is slower than “just add a backend.” It is also more honest.
Because the promise of Vibecodr is not that user code can do anything with no boundaries. The promise is that people can make things that feel alive, publish them into a social runtime, and trust the platform to take boundaries seriously enough that those things can be experienced safely.
That is what is coming.
Not just more power.
A better shape for power.
Braden